
Collect the latest CompTIA CAS-003 exam exercise questions and valid tips!
CompTIA latest exam tips 2020! ExamSall offers the latest CAS-003 exam exercise questions, CAS-003 pdf, the CAS-003 free exam to help you improve your skills! Improve the exam to pass! Lea4pass is our partner and they have the most authoritative testing experts! Easily pass the exam,
select the complete CompTIA CAS-003 exam dumps https://www.leads4pass.com/cas-003.html The latest updated exam dump.
Guaranteed to be effective and authentic! leads4pass year-round updates ensure your first exam passes!
ExamSall Exam Table of Contents:
- Latest CompTIA CAS-003 google drive
- Effective CompTIA CAS-003 exam practice questions
- leads4pass Year-round Discount Code
- What are the advantages of leads4pass?
Latest CompTIA CAS-003 google drive
[PDF] Free CompTIA CAS-003 pdf dumps download from Google Drive: https://drive.google.com/file/d/1JEE4WM1XAEy-1G6jhd-qu6_rjKfaZAZd
CompTIA Advanced Security Practitioner (CASP+)
EXAM CODE CAS-003: https://www.comptia.org/certifications/comptia-advanced-security-practitioner
CASP+ covers the technical knowledge and skills required to conceptualize, engineer, integrate and implement secure solutions
across complex environments to support a resilient enterprise.
Latest updates CompTIA CAS-003 exam practice questions
QUESTION 1
After a large organization has completed the acquisition of a smaller company, the smaller company must implement
new host-based security controls to connect its employees\’ devices to the network. Given that the network requires
802.1X EAP-PEAP to identify and authenticate devices, which of the following should the security administrator do to
integrate the new employees\’ devices into the network securely?
A. Distribute a NAC client and use the client to push the company\’s private key to all the new devices.
B. Distribute the device connection policy and a unique public/private key pair to each new employee\’s device.
C. Install a self-signed SSL certificate on the company\’s RADIUS server and distribute the certificate\’s public key to
all new client devices.
D. Install an 802.1X supplicant on all new devices and let each device generate a self-signed certificate to use for
network access.
Correct Answer: D
QUESTION 2
The Information Security Officer (ISO) believes that the company has been targeted by cybercriminals and it is under a
cyber attack. Internal services that are normally available to the public via the Internet are inaccessible, and employees
in the office are unable to browse the Internet. The senior security engineer starts by reviewing the bandwidth at the
border router, and notices that the incoming bandwidth on the router\’s external interface is maxed out. The security engineer then inspects the following piece of log to try and determine the reason for the downtime, focusing on the
company\’s external router\’s IP which is 128.20.176.19:
11:16:22.110343 IP 90.237.31.27.19 > 128.20.176.19.19: UDP, length 1400 11:16:22.110351 IP 23.27.112.200.19 >
128.20.176.19.19: UDP, length 1400 11:16:22.110358 IP 192.200.132.213.19 > 128.20.176.19.19: UDP, length 1400
11:16:22.110402 IP 70.192.2.55.19 > 128.20.176.19.19: UDP, length 1400 11:16:22.110406 IP 112.201.7.39.19 >
128.20.176.19.19: UDP, length 1400 Which of the following describes the findings the senior security engineer should
report to the ISO and the BEST solution for service restoration?
A. After the senior engineer used a network analyzer to identify an active Fraggle attack, the company\’s ISP should be
contacted and instructed to block the malicious packets.
B. After the senior engineer used the above IPS logs to detect the ongoing DDOS attack, an IPS filter should be
enabled to block the attack and restore communication.
C. After the senior engineer used a mirror port to capture the ongoing amplification attack, a BGP sinkhole should be
configured to drop traffic at the source networks.
D. After the senior engineer used a packet capture to identify an active Smurf attack, an ACL should be placed on the
company\’s external router to block incoming UDP port 19 traffic.
Correct Answer: A
The exhibit displays logs that are indicative of an active Fraggle attack. A Fraggle attack is similar to a smurf attack in
that it is a denial of service attack, but the difference is that a Fraggle attack makes use of ICMP and UDP ports 7 and
Thus when the senior engineer uses a network analyzer to identify the attack he should contact the company\’s ISP
to block those malicious packets.
QUESTION 3
A company has decided to replace all the T-1 uplinks at each regional office and move away from using the existing
MPLS network. All regional sites will use high-speed connections and VPNs to connect back to the main campus. Which
of the following devices would MOST likely be added at each location?
A. SIEM
B. IDS/IPS
C. Proxy server
D. Firewall
E. Router
Correct Answer: D
QUESTION 4
A penetration tester has been contracted to conduct a physical assessment of a site. Which of the following is the
MOST plausible method of social engineering to be conducted during this engagement?
A. Randomly calling customer employees and posing as a help desk technician requiring user password to resolve
issues
B. Posing as a copier service technician and indicating the equipment had “phoned home” to alert the
C. technician for a service call
D. Simulating an illness while at a client location for a sales call and then recovering once listening devices are installed
E. Obtaining fake government credentials and impersonating law enforcement to gain access to a company facility
Correct Answer: A
QUESTION 5
A security administrator is concerned about the increasing number of users who click on malicious links contained within
phishing emails. Although the company has implemented a process to block these links at the network perimeter, many
accounts are still becoming compromised. Which of the following should be implemented to further reduce the number
of account compromises caused by remote users who click these links?
A. Anti-spam gateways
B. Security awareness training
C. URL rewriting
D. Internal phishing campaign
Correct Answer: B
QUESTION 6
A software development team has spent the last 18 months developing a new web-based front-end that will allow clients
to check the status of their orders as they proceed through manufacturing. The marketing team schedules a launch
party to present the new application to the client base in two weeks. Before the launch, the security team discovers
numerous flaws that may introduce dangerous vulnerabilities, allowing direct access to a database used by
manufacturing. The development team did not plan to remediate these vulnerabilities during development.
Which of the following SDLC best practices should the development team have followed?
A. Implementing regression testing
B. Completing user acceptance testing
C. Verifying system design documentation
D. Using an SRTM
Correct Answer: D
QUESTION 7
An internal application has been developed to increase the efficiency of the operational process of a global
manufacturer. A new code was implemented to fix a security bug, but it has caused operations to halt. The executive
team has decided fixing the security bug is less important than continuing operations.
Which of the following would BEST support immediate rollback of the failed fix? (Choose two.)
A. Version control
B. Agile development
C. Waterfall development
D. Change management
E. Continuous integration
Correct Answer: AD
QUESTION 8
A security analyst is reviewing the following company requirements prior to selecting the appropriate technical control
configuration and parameter:
RTO:2 days RPO:36 hours MTTR:24 hours MTBF:60 days
Which of the following solutions will address the RPO requirements?
A. Remote Syslog facility collecting real-time events
B. Server farm behind a load balancer delivering five-nines uptime
C. A backup solution that implements daily snapshots
D. Cloud environment distributed across geographic regions
Correct Answer: C
QUESTION 9
A security engineer is employed by a hospital that was recently purchased by a corporation. Throughout the acquisition
process, all data on the virtualized file servers must be shared by departments within both organizations. The security
engineer considers data ownership to determine:
A. the amount of data to be moved.
B. the frequency of data backups.
C. which users will have access to which data
D. when the file server will be decommissioned
Correct Answer: C
QUESTION 10
A security engineer successfully exploits an application during a penetration test. As proof of the exploit, the security
engineer takes screenshots of how data was compromised in the application. Given the information below from the
screenshot.
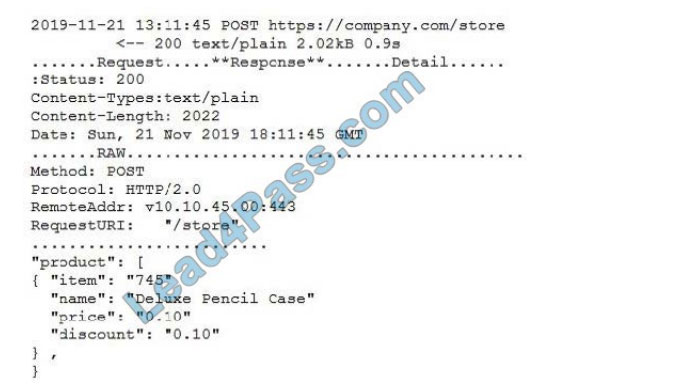
Which of the following tools was MOST likely used to exploit the application?
A. The engineer captured the data with a protocol analyzer, and then utilized Python to edit the data
B. The engineer queried the server and edited the data using an HTTP proxy interceptor
C. The engineer used a cross-site script sent via curl to edit the data
D. The engineer captured the HTTP headers, and then replaced the JSON data with a banner-grabbing tool
Correct Answer: B
QUESTION 11
A user is suspected of engaging in potentially illegal activities. Law enforcement has requested that the user continue to
operate on the network as normal. However, they would like to have a copy of any communications from the user
involving certain key terms. Additionally, the law enforcement agency has requested that the user\’s ongoing
communication be retained in the user\’s account for future investigations. Which of the following will BEST meet the
goals of law enforcement?
A. Begin a chain-of-custody on for the user\’s communication. Next, place a legal hold on the user\’s email account.
B. Perform an e-discovery using the applicable search terms. Next, back up the user\’s email for a future investigation.
C. Place a legal hold on the user\’s email account. Next, perform e-discovery searches to collect applicable emails.
D. Perform a back up of the user\’s email account. Next, export the applicable emails that match the search terms.
Correct Answer: C
A legal hold is a process that an organization uses to maintain all forms of pertinent information when legal action is
reasonably expected. E-discovery refers to discovery in litigation or government investigations that manages the
exchange of electronically stored information (ESI). ESI includes email and office documents, photos, videos, databases,
and other filetypes.
QUESTION 12
Ann, a systems engineer, is working to identify an unknown node on the corporate network. To begin her investigative
work, she runs the following Nmap command string: user@hostname:~$ Sudo Nmap 192.168.1.54 Based on the output,
Nmap is unable to identify the OS running on the node, but the following ports are open on the device: TCP/22 TCP/111
TCP/512-514 TCP/2049 TCP/32778 Based on this information, which of the following operating systems is MOST likely
running on the unknown node?
A. Linux
B. Windows
C. Solaris
D. OSX
Correct Answer: C
TCP/22 is used for SSH; TCP/111 is used for Sun RPC; TCP/512-514 is used by CMD like exec, but automatic
authentication is performed as with a login server, etc. These are all ports that are used when making use of the Sun
Solaris operating system.
QUESTION 13
Ann, a member of the finance department at a large corporation, has submitted a suspicious email she received to the
information security team. The team was not expecting an email from Ann, and it contains a PDF file inside a ZIP
compressed archive. The information security learn is not sure which files were opened. A security team member uses
an air-gapped PC to open the ZIP and PDF, and it appears to be a social engineering attempt to deliver an exploit.
Which of the following would provide greater insight on the potential impact of this attempted attack?
A. Run an antivirus scan on the finance PC.
B. Use a protocol analyzer on the air-gapped PC.
C. Perform reverse engineering on the document.
D. Analyze network logs for unusual traffic.
E. Run a baseline analyzer against the user\’s computer.
Correct Answer: B
Latest leads4pass Year-round Discount Code 2020

Why leads4pass is the industry leader
leads4pass has many years of exam experience! Finishing school is your goal! Getting good employment conditions is your goal!
Our goal is to help more people pass the CompTIA exam! Exams are a part of life but important! In the study you need to make great efforts to sum up the study! Trust leads4pass if you can’t easily pass because of exam details!
We have the most authoritative CompTIA exam experts! The most efficient pass rate! We are the industry leader!
Latest update leads4pass CAS-003 exam dumps: https://www.leads4pass.com/cas-003.html (532 Q&As)
[Q1-Q12 PDF] Free CompTIA CAS-003 pdf dumps download from Google Drive: https://drive.google.com/file/d/1JEE4WM1XAEy-1G6jhd-qu6_rjKfaZAZd
Summarize:
This blog shares the latest CompTIA CAS-003 exam dumps, CAS-003 exam questions, and answers! CAS-003 pdf, CAS-003 exam video!
You can also practice the test online! leads4pass is the industry leader!
Select leads4pass CAS-003 exams Pass CompTIA CAS-003 exams “CompTIA Advanced Security Practitioner (CASP)”. Help you successfully pass the CAS-003 exam.